Followup on
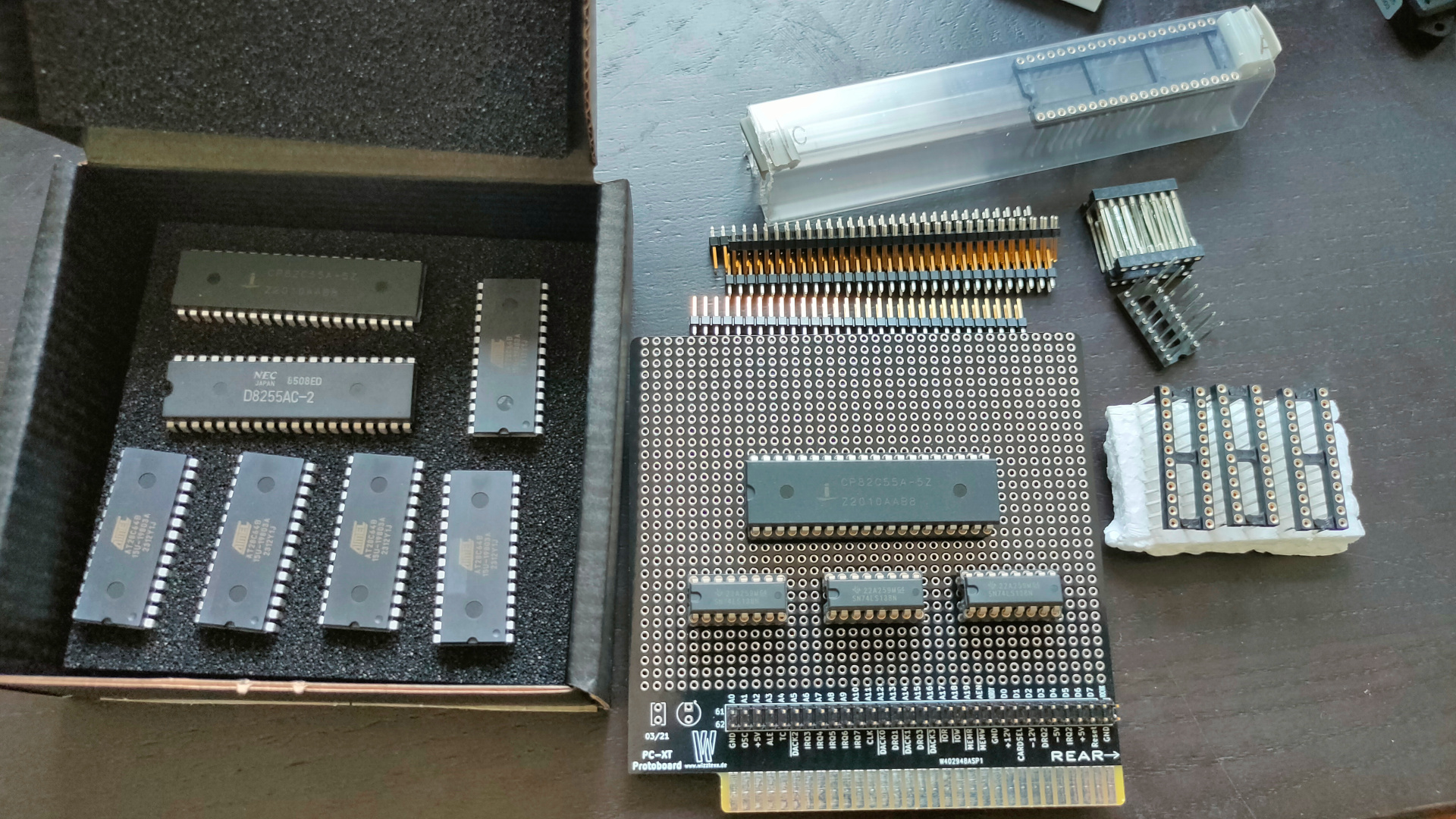
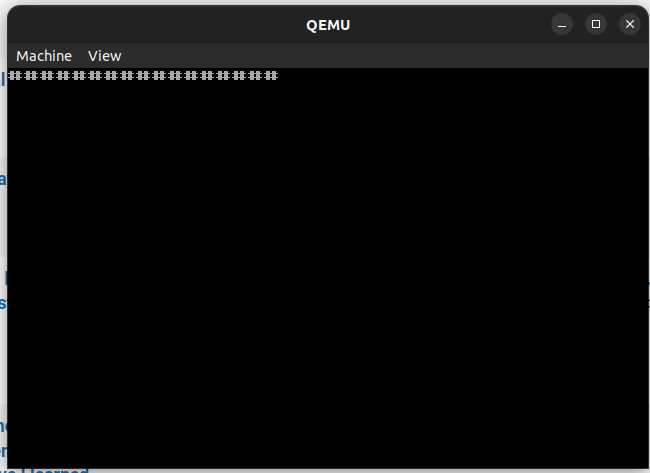
Today two boot projects.
One using a bios extension, so it chip based.
Second is a floppy disk boot program. (Creating a test situation to get our old Boot floppy demo working. ( That one without using an operatingsystem like ms-dos.
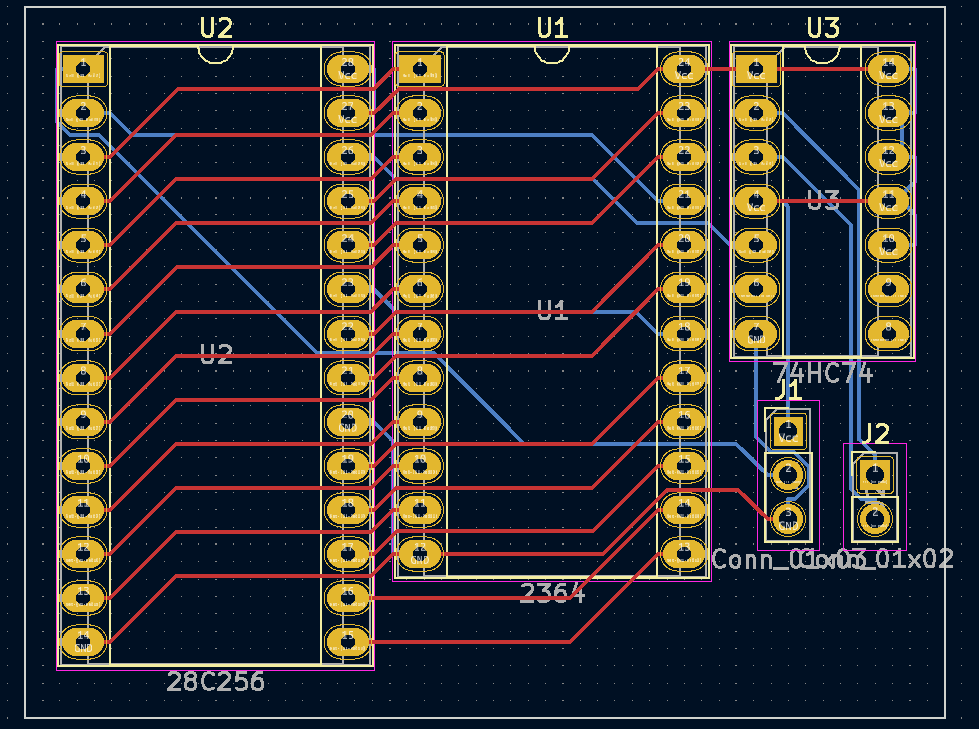
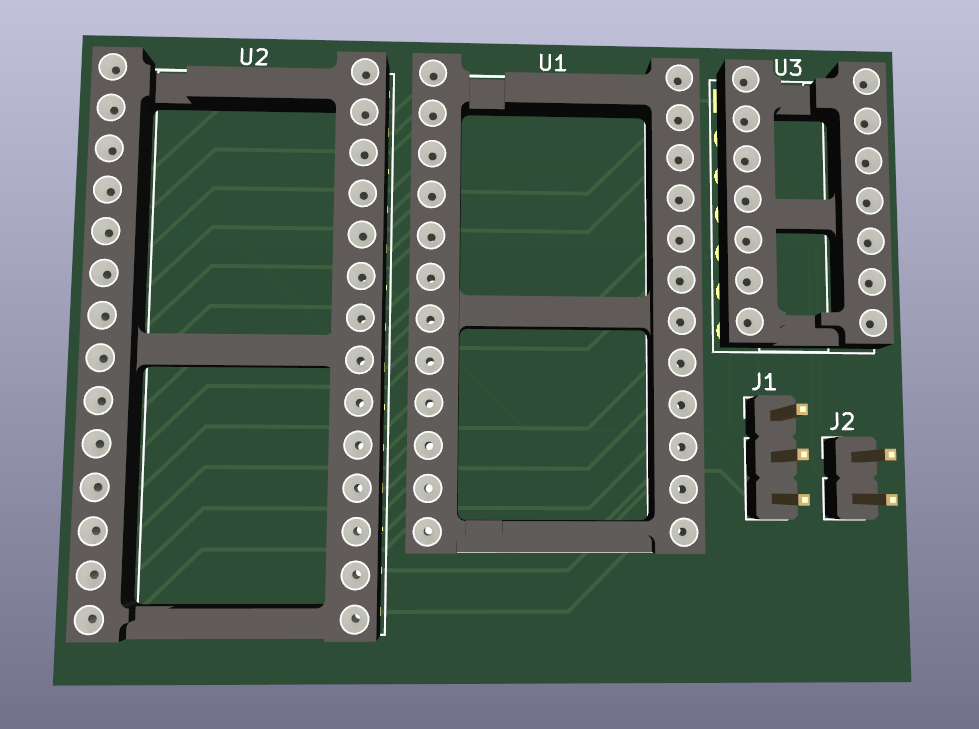
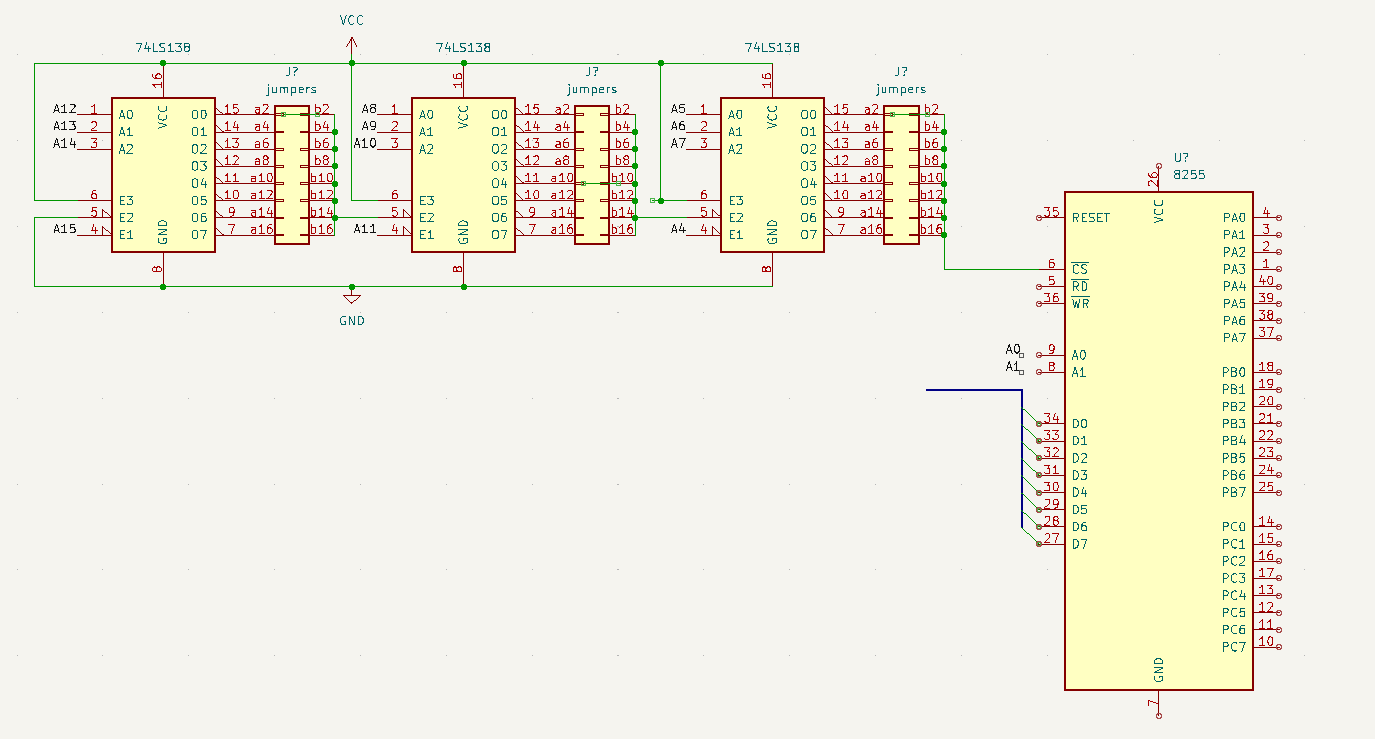
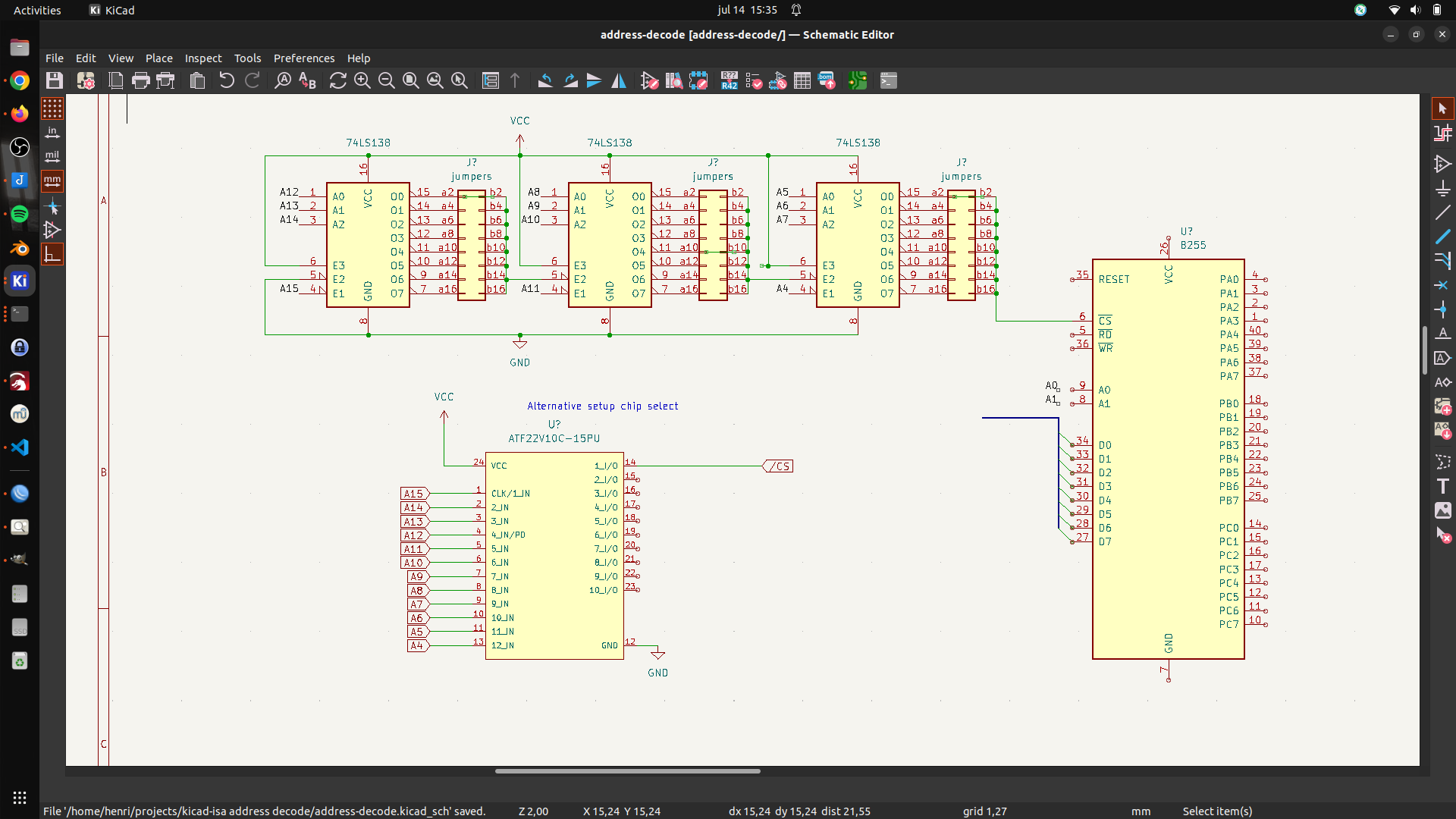
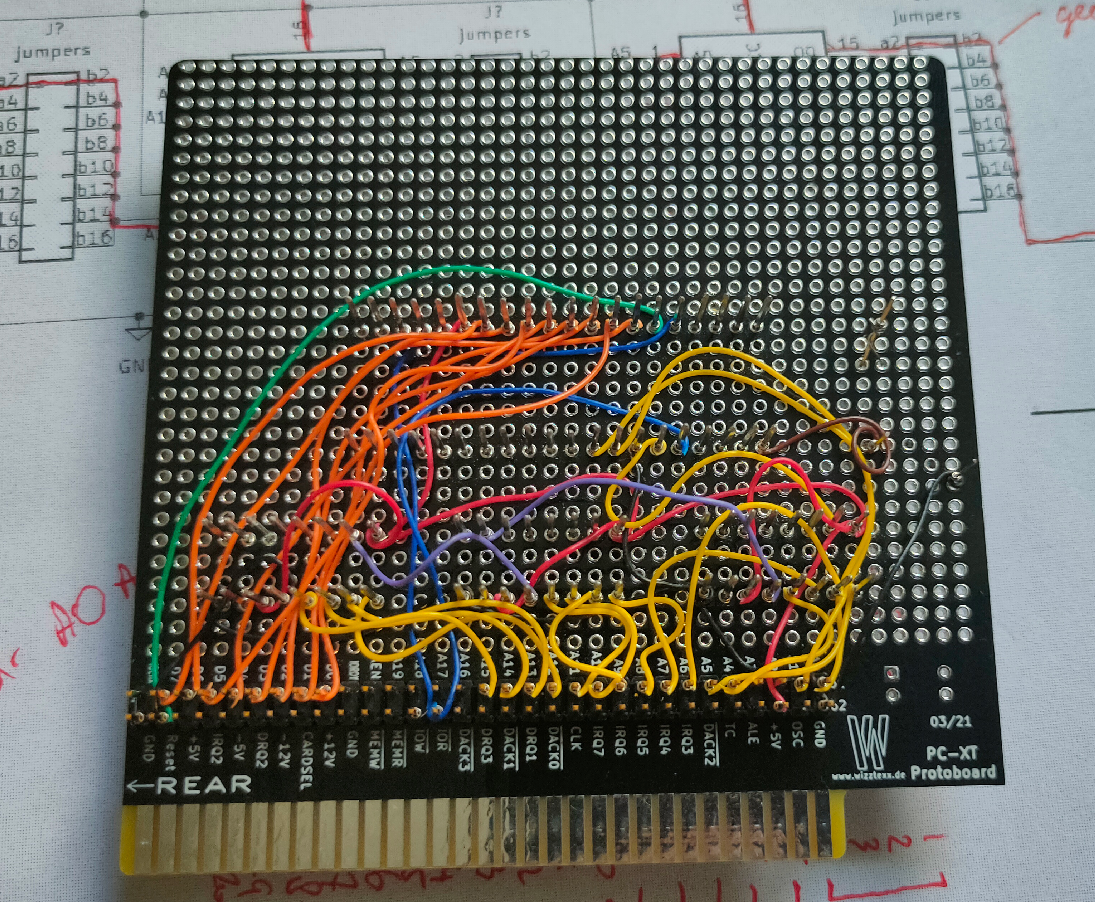
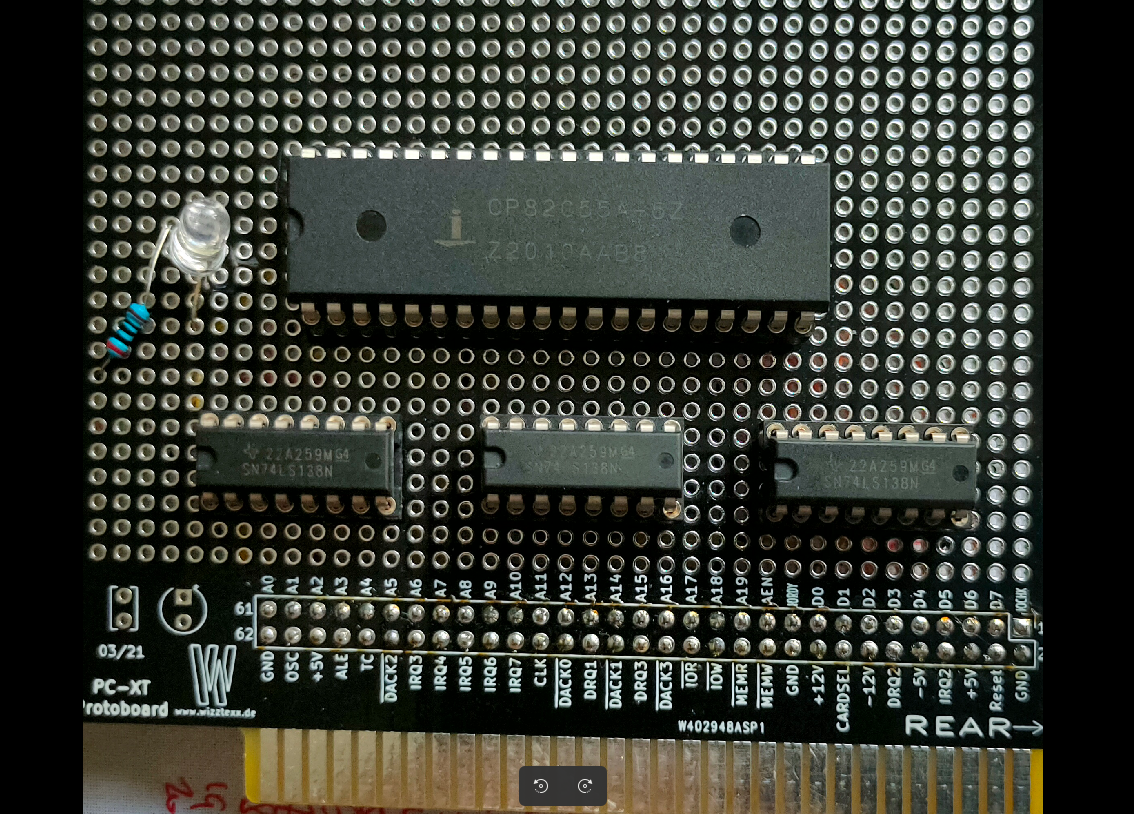
Creating a Secondary Bios ROM
NAME mycode
.model small
ORG 0h
.code
dw 0AA55h ; Magic header your bios is looking for
db 16 ; lenght of this rom in 512 bytes == 8k
jmp short clear ; jmp to program
ORG 20h ; start of program
clear: mov cx,10 ; clear, set keyboard led and print 10 # chars
mov ah,0ah
mov al,31h
int 10h
mov bh,0
mov cx,1
start: mov al, 11000000b
out 80h, al
print: mov cx,10
mov ah,0ah
mov al,"#"
int 10h
loop1: nop ; loop until doomsday
jmp loop1
db -68 ; This makes the checksum 0
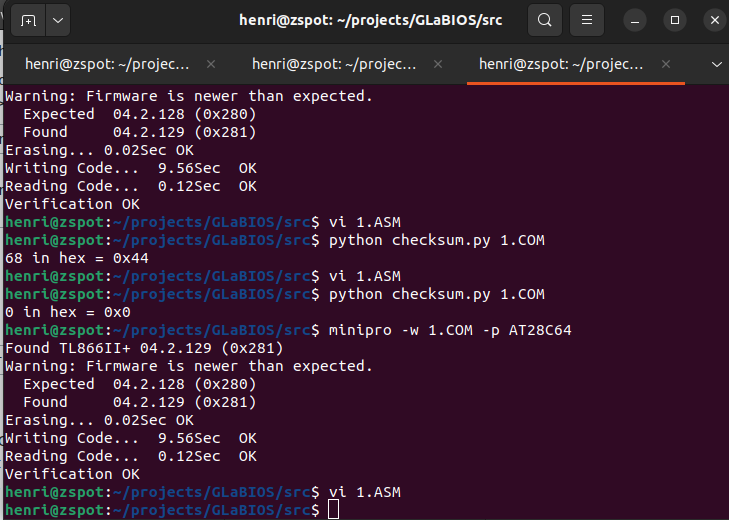
; steps to take: edit source, make this byte entry 0
; compile using make.bat in dosbox
; check checksum using my python script
; output was 68 hex 0x44
; edit asm file place -68 to make the checksum 0x00 again
; compile and burn to ROM
ORG 2000h ; create end of rom 0000h-1fffh = 8K
END
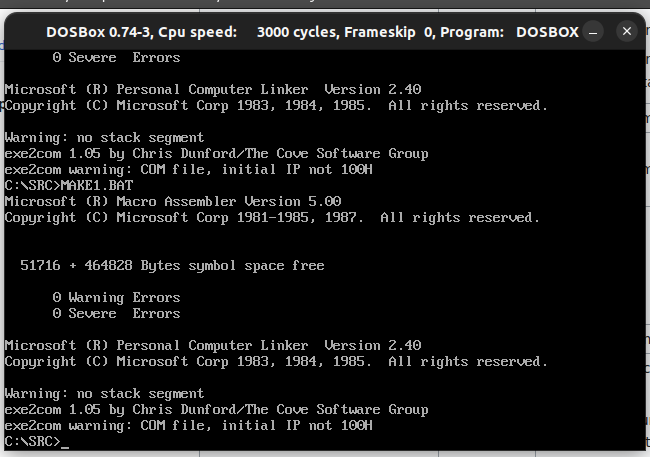
make.bat in dosbox
@ECHO OFF MASM /DARCH_TYPE="T" /DCPU_TYPE="V" 1; LINK 1; EXE2COM 1.EXE
Python script here: https://www.henriaanstoot.nl/2023/06/20/bios-hacking/
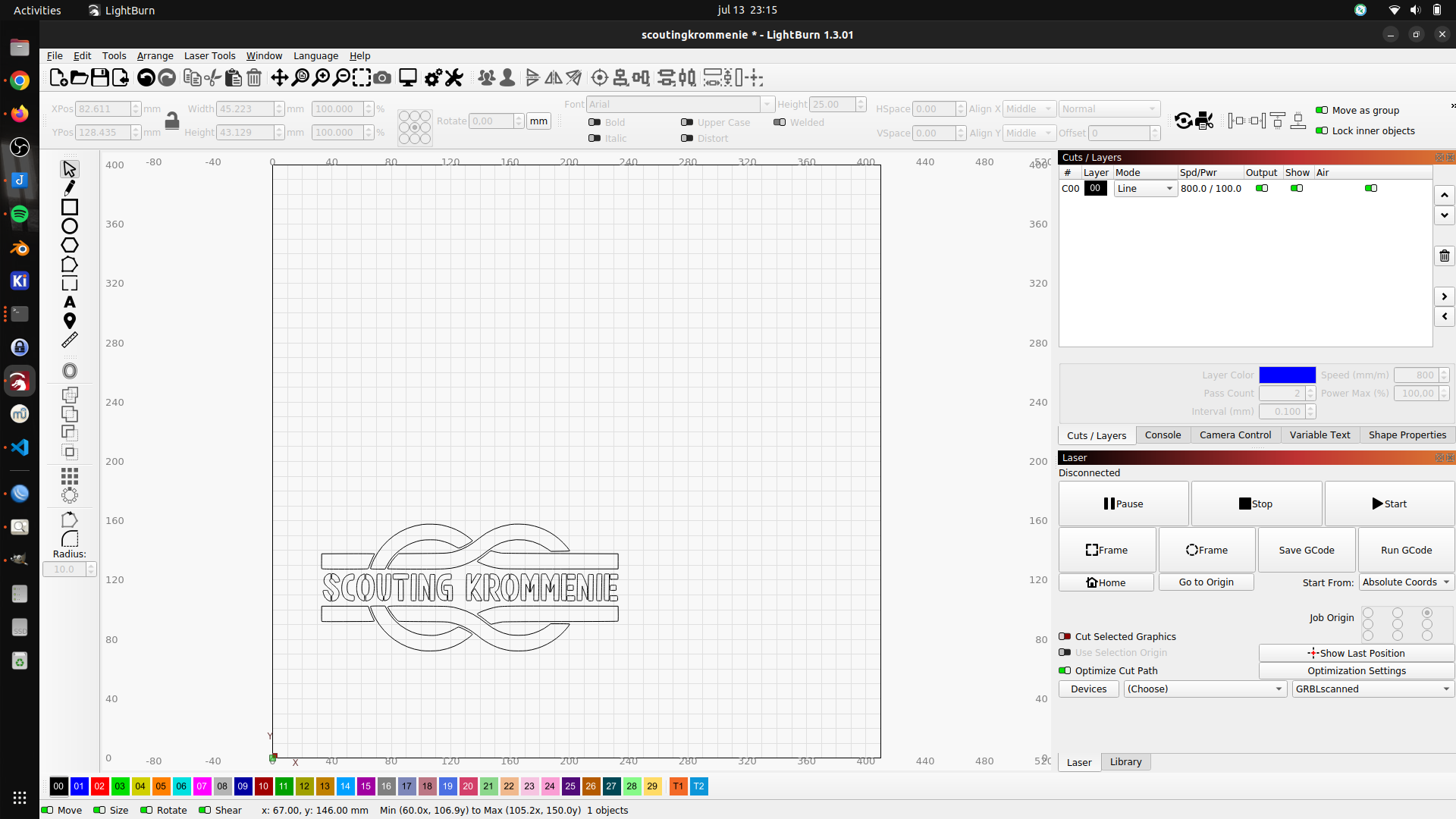
Write EEprom
minipro -w 1.COM -p AT28C64
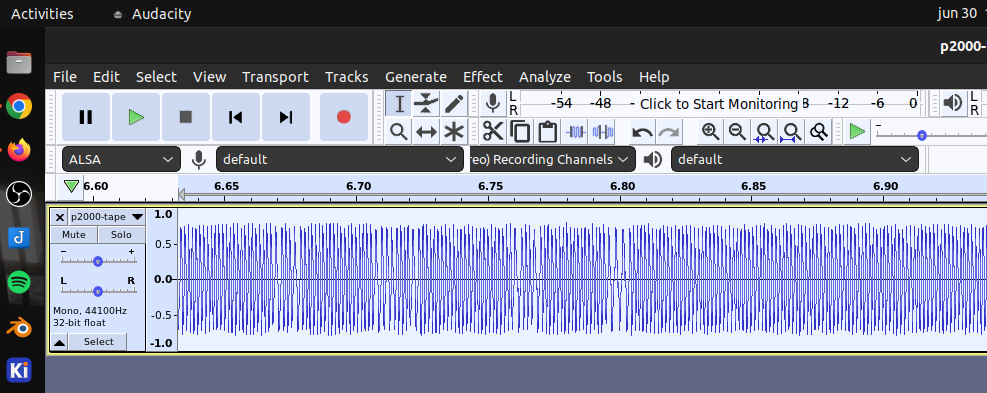
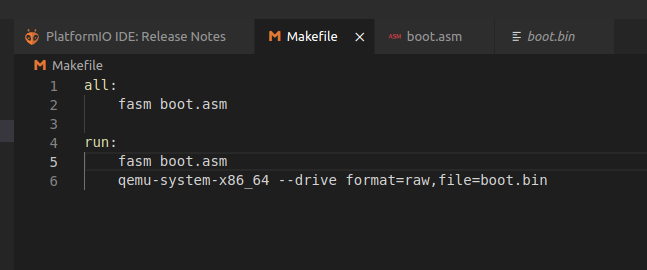
Part 2 – Bootsector program !
Allmost the same as above, but booting from a Floppy disk.
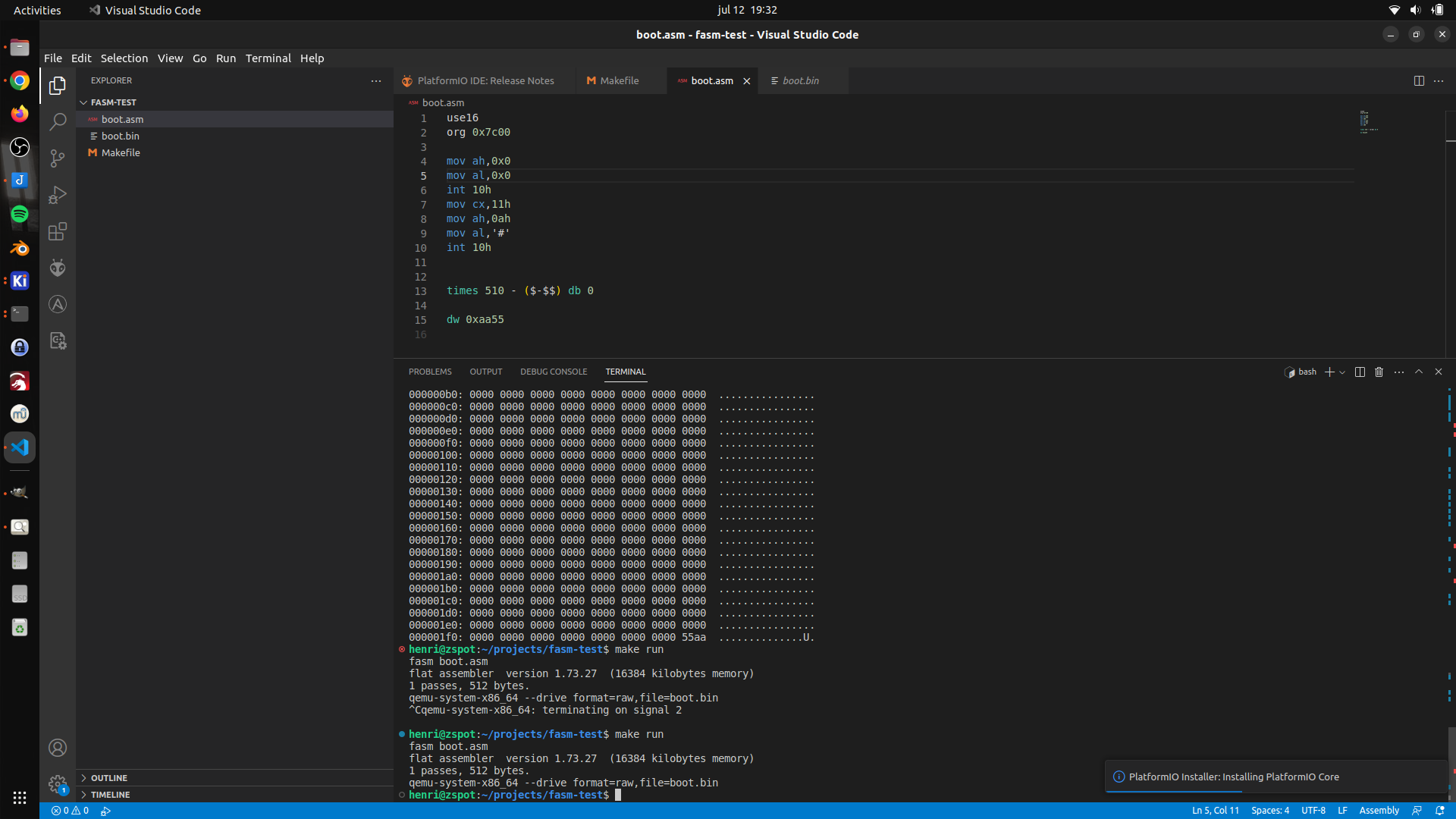
Video mode info : https://stanislavs.org/helppc/int_10-0.html
Assembly code
use16 ; 16 bits org 0x7c00 ; start address ( change? ) mov ah,0x0 ; ah 0h - video mode mov al,0x0 ; al 0h - mode 0 - 40x25 chars int 10h ; scree routines mov cx,11h ; 11 chars mov ah,0ah ; ah 0ah - print char mode mov al,'#' ; choose char as # int 10h ; execute times 510 - ($-$$) db 0 ; fill rest 512 bytes sector dw 0xaa55 ; magic bytes